Notification Policies Common Fields
The following are suggested templates that can be used to notify the Admin team and end users.
For more details about notification policies, see Creating a Notification Policy for a Rule.
For a description of common fields that can be used in notification policies and other custom notifications,
Default Notification Policy Templates
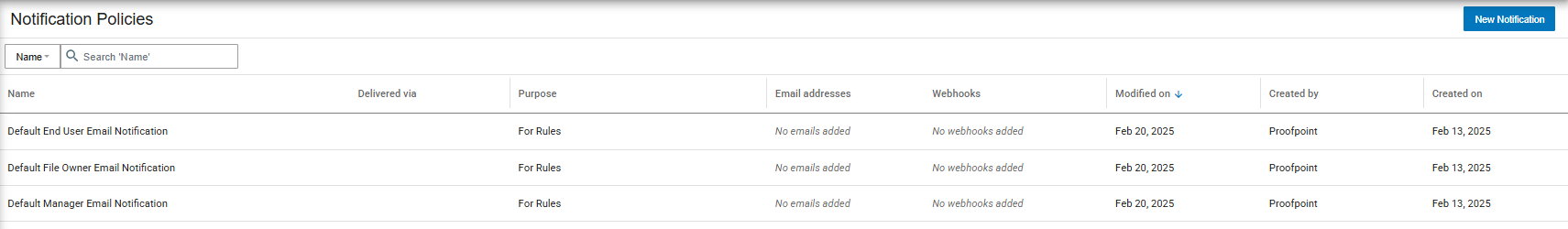
Four Out-of-the-Box notification policies are available (Integrations > Notification Policies):
-
Default Admin Email Notification: Notify administrators about a security incident.
By default, all users with Full Administration access policy are notified. To specify recipients, create a custom notification policy using the Admin template. See:
-
Default End User Email Notification: Notify end users about a security incident they were involved in.
-
Default Manager Email Notification: Notify an end-user’s manager (as specified in Active Directory) about a security alert involving their user.
Cloud DLP Admin Notification\ATO Protection Suggested Template
This suggested template can be used to notify the team provisioning the solution about new alerts.
| Recipients | Set the recipients based on your needs |
| Subject |
{{event.entity.suite}} Alert from Proofpoint team - {{event.incident.name}} |
| Body |
Dear Admin, An alert for the following activity was generated: {{event.incident.name}} {{#if event.resources}} File: {{event.resources.[0].name}} {{/if}} Alert Severity: {{stringLastElementByDelimiter event.incident.severity delimiter=':'}} User: {{event.user.email}} Cloud Service: {{event.entity.suite}} Alert Time: {{event.event.createdAt}} Event Time: {{event.event.occurredAt}} User Agent: {{#if event.remote.client.agent.description}}{{event.remote.client.agent.description}}{{else}}N\A{{/if}} Device: {{#if event.remote.client.device.kind}} {{stringLastElementByDelimiter event.remote.client.device.kind delimiter=':'}}{{else}}N\A{{/if}}
{{#filter event.indicators "pfpt:cloud:threat" property="kind"}}
Risk Assessment: ------------------------ Risk Level: {{stringLastElementByDelimiter this.risk.level delimiter=':'}} Description: {{#if this.description}}{{this.description}}{{else}}{{this.name}}{{/if}}{{/filter}}{{#if event.intelligence.findings}}
Findings: {{#each event.intelligence.findings}}{{#if @index}}, {{/if}}{{translateEnumValue this.kind "intelligence:findings:kind" ../options.translationMapping}}{{/each}}{{/if}}{{#if (some event.indicators "kind" "pfpt:cloud:threat")}}{{#unless alert.remediation.type}} Reduce attacker dwell time with instant automated remediation. View recommended actions in Policy->Rule Editor->Rule Templates{{/unless}}{{/if}}
To find more regarding this alert, please click <a href={{#if config.vanityExploreZoneName}}https://{{event.feed.details.tenant.alias}}.{{config.vanityExploreZoneName}}{{else}}{{config.externalURL}}{{/if}}{{#if event.incident}}/v2/apps/search/incidents/new/search?fqid={{else}}/v2/apps/search/activities/new/search?fqid={{/if}}{{event.fqid}}&region={{event.feed.region}}>here</a>
Thank you, The Proofpoint team |
Cloud DLP End-User Notification
This suggested template can be used to notify end-users about alerts that were triggered related to their activities.
| Recipients | {{event.user.email}} |
| Subject |
{{event.entity.suite}} Alert from Proofpoint team - {{event.incident.name}} |
| Body |
Dear {{event.user.displayName}}, An alert for your following activity was generated: {{event.incident.name}} {{#if event.resources}} File: {{event.resources.[0].name}} {{/if}} Alert Severity: {{stringLastElementByDelimiter event.incident.severity delimiter=':'}} User: {{event.user.email}} Cloud Service: {{event.entity.suite}} Alert Time: {{event.event.createdAt}} Event Time: {{event.event.occurredAt}} User Agent: {{#if event.remote.client.agent.description}}{{event.remote.client.agent.description}}{{else}}N\A{{/if}} Device: {{#if event.remote.client.device.kind}}{{stringLastElementByDelimiter event.remote.client.device.kind delimiter=':'}}{{else}}N\A{{/if}}
{{#filter event.indicators "pfpt:cloud:threat" property="kind"}} Risk Level: {{stringLastElementByDelimiter this.risk.level delimiter=':'}} Description: {{#if this.description}}{{this.description}}{{else}}{{this.name}}{{/if}}{{/filter}}
Thank you, The Proofpoint team |
Notification Policies Common Fields
Notification Policies can be set up to send notifications via customized emails. These customized email notifications allow you to send as many notifications as needed to multiple defined users with your specified text.
| Field Name | Notification Parameter |
|---|---|
| Alert Name | {{event.incident.name}} |
| Alert Severity | {{stringLastElementByDelimiter event.incident.severity delimiter=':'}} |
| Alert Time | {{event.event.createdAt}} |
| Event Time | {{event.event.occurredAt}} |
| Event Name | {{stringLastElementByDelimiter event.activity.primaryCategory delimiter=':'}} |
| User Email | {{event.user.email}} |
| User Name | {{event.user.displayName}} |
| User’s Manager (for M365 only) | {{stringLastElementByDelimiter event.user.directory.manager.aliases.value delimiter=':'}} |
| File Name | {{event.resources.[0].name}} |
| File Host | {{event.resources.[0].container.name}} |
| File Path | {{event.resources.[0].path}} |
| File Owner | {{event.resources.[0].owner.user.name}} |
| File’s Share Level | {{stringLastElementByDelimiter event.resources.[0].permissions.share.level.designation delimiter=':'}} |
|
Third Party App Name (CASB only) |
{{event.activity.api.resources.[0].name}} |
|
Suspicious Login Severity (CASB only) |
{{#filter event.indicators "pfpt:cloud:threat" property="kind"}}{{stringLastElementByDelimiter this.risk.level delimiter=':'}} {{/filter}} |
|
Intelligence Findings Types (CASB only) |
{{#if event.intelligence.findings}}{{#each event.intelligence.findings}}{{#if @index}}, {{/if}}{{translateEnumValue this.kind "intelligence:findings:kind" ../options.translationMapping}}{{/each}}{{/if}} |
Related Topic: