What data is at risk?
Risks are identified with a Risk Signature and Risk ID. Each risk is generated for the specific entity on a per cloud basis to ensure that Cloud provider specific risk information is shown.
What is a Risk Signature?
A risk signature is a specific path in the graph of your cloud asset configurations, access, and data.
Every asset or resource that is detected to have any potential configuration or data related issue is categorized based on the corresponding Risk Signature that matches the issue.
The information icon (circled i) next to each risk description provides details and steps to remediate it. Users can download the information in CSV format which can be used for reviewing the account-based risk items, risk signature-based items, or resource-based risk items.
Risk definition from a cloud or hybrid perspective can be classified in two categories:
Configuration Risks
Configuration risks refer to the potential threats or vulnerabilities arising from the improper setup or configuration of hardware, software, networks, or systems. These risks can result in security breaches, data loss, system downtime, and other adverse consequences. Common examples of configuration risks include using default or weak passwords, misconfiguring access controls, leaving unnecessary ports open, and not applying necessary security updates or patches (package vulnerabilities), etc.
Data Risks
Data risks pertain to the threats and vulnerabilities associated with the handling, storage, and transmission of sensitive information. This includes both personal and organizational data. Data risks can lead to unauthorized access, data breaches, data manipulation, data loss, and privacy violations. Factors contributing to data risks include inadequate encryption, lack of data backup and disaster recovery plans, weak access controls.
The myriad of data, configuration and the risks associated with the entities, assets on Cloud or Hybrid applications necessitate staying informed about threats and maintaining up-to-date security measures to thwart any unauthorized access to data.
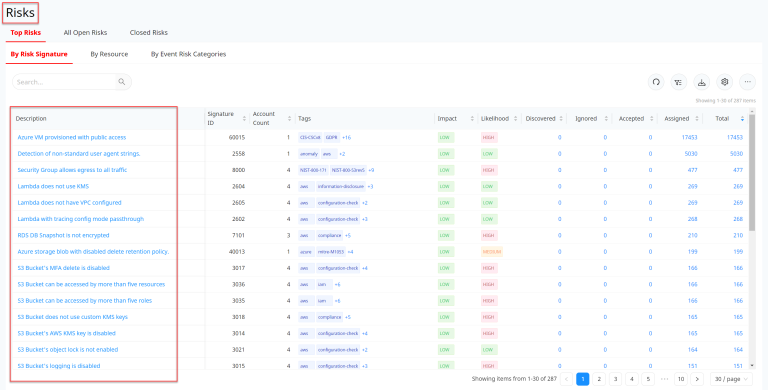
The Risks section is divided in three categories:
- Top Risks
- All Open Risks
- Closed Risks