Risk signatures refer to patterns, indicators, or characteristics that are used to identify potential security risks, vulnerabilities, or threats
What is a Risk Signature?
A risk signature is a specific path in the graph of your cloud asset configurations, access and data.
For example, a risk signature could instruct DSPM to look for servers that have open SSH access that have full sync access to an S3 bucket containing PII data.
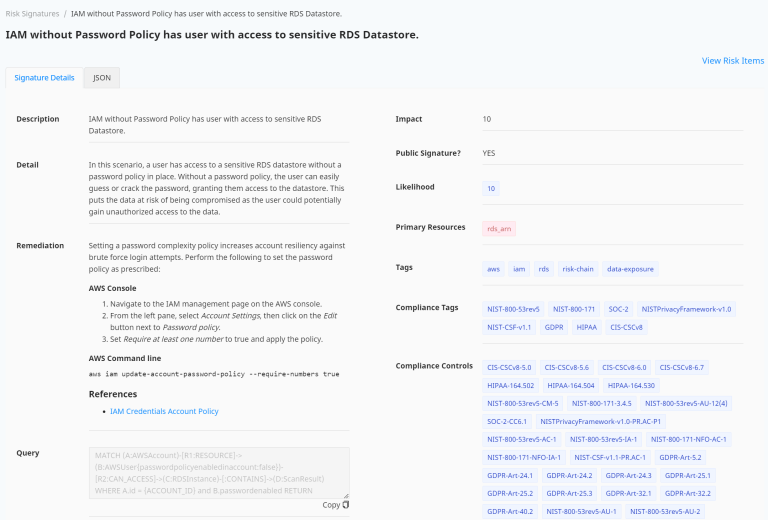
Each signature is assigned a unique ID which is attached to the entities during data scan operation.
For each Risk Signature, it’s associated Query too is displayed which would be used to retrieve the resources, entities for which the Risks are defined.
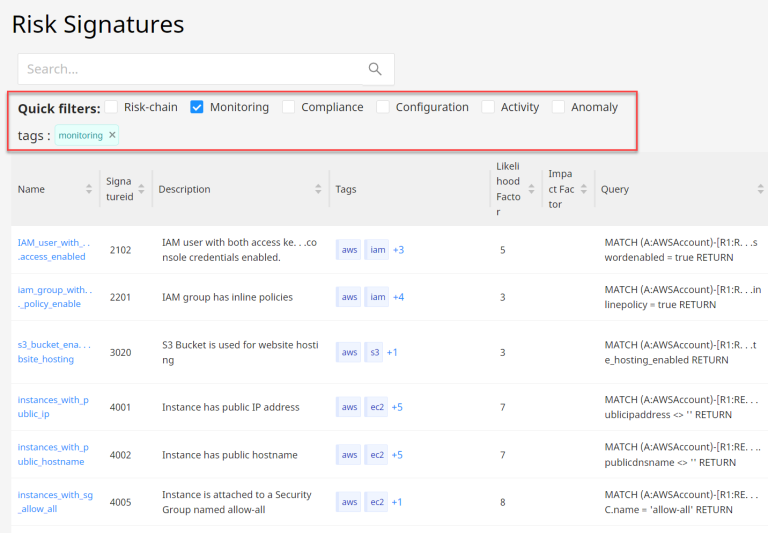
Quick Filters
Select any combination of Quick Filters to focus the list view:
- Risk-chain
- Monitoring
- Compliance
- Configuration
- Activity
- Anomaly