Vulnerability scanner captures the details for all the packages installed on the machine (EC2, Azure VM, GCP Compute Engine, ECR) by the host OS or any of the applications that are installed on it.
The details are then categorized and checked against the NVD database, and if there are any CVE for the application and the respective versions, these are captured and listed.
Along with the CVE details, if there are any of the GHSA events linked to the packages, these are captured and listed as well.
Vulnerability Scan can be enabled or disabled at the time of account onboarding or afterwards by editing the account.
The most important aspect for the instances to be scanned is that only snapshots created from EBS Volume (AWS) and Disks (Azure) which are attached to an EC2 instance and Azure VM are selected for vulnerability scan.
The details for the CVEs are available on DSPM in the form of information icon (i) for each of the listed items.
For each of the packages, the OS details, FQDN and the parent application name are captured and listed.
This scanner task is automated and runs every 12 hours based on a combination onboarding time and the cloud account identifier (for AWS-Account ID, for Azure-Subscription ID, for GCP-Project ID)
To list all the EBS Volumes that are eligible for Vulnerability Scan, use the Query Builder feature.
Steps to list all the volumes use the following query from the builder:
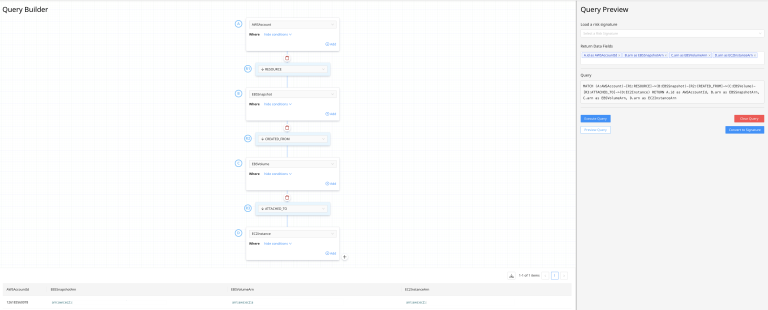
The query for the above operation is as follows:
// MATCH (A:AWSAccount)-[R6:RESOURCE]->(G:EBSSnapshot)-[R7:CREATED_FROM]->(H:EBSVolume)-[R8:ATTACHED_TO]->(I:EC2Instance) RETURN A.id as AWSAccountId, G.arn as EBSSnapshotArn, H.arn as EBSVolumeArn, I.arn as EC2InstanceArnAny EBS volumes that are not listed from the above query will not be available for the Vulnerability scanner task to pick up.
Similarly for AzureDisks, the corresponding query to look up is as follows:
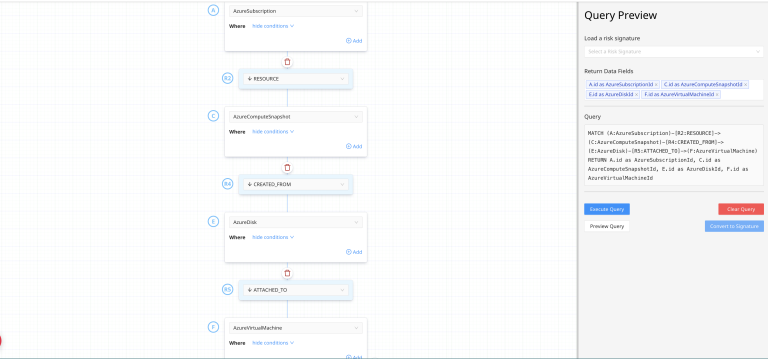
The query for the above operation is as follows:
// MATCH (A:AzureSubscription)-[R2:RESOURCE]->(C:AzureComputeSnapshot)-[R4:CREATED_FROM]->(E:AzureDisk)-[R5:ATTACHED_TO]->(F:AzureVirtualMachine) RETURN A.id as AzureSubscriptionId, C.id as AzureComputeSnapshotId, E.id as AzureDiskId, F.id as AzureVirtualMachineIdCurrently, Vulnerablility scanner supports only AWS EC2 instances, ECR and Azure Virtual Machine instances.